Election Officials Toolkit for Technical Volunteers
From epollbook connection errors to ballot marking device touchscreen miscalibration, technical issues are leading to long lines and decreased voter confidence in elections. At the same time, younger voters are becoming engaged in the electoral process for the first time. Local and state officials can leverage this enthusiasm by identifying a new roles for digital native volunteers who have grown up with mobile devices and social media networks. Civic-minded community members with technical skills or IT support experience can combine their knowledge and talents as technical volunteers for Election Day and beyond.
Polling locations with modern equipment such as epollbooks, ballot marking devices, and precinct scanners require technical volunteers who are comfortable setting up, operating, and troubleshooting them. Voters can sense stressful situations when equipment is not working properly, and that has a negative impact on voter confidence. The information below will help you understand where to find these Information Security (infosec) professionals and how you can get them involved as technical volunteers.
Volunteer Roles
Modern voting equipment is becoming increasingly more complex and can be difficult to operate and troubleshoot for users that are not technically-savvy. Today’s volunteers are being asked to perform functions that are much more technical in nature. It is unreasonable to expect to train all existing volunteers to be more proficient with operating and troubleshooting all of the equipment. What’s more, dedicated technical repair teams can be quickly overwhelmed when things go wrong. Delays can compound depending on the travel time between locations and prioritization of issues.
Consider how a technical volunteer at every polling location can fill this critical need by ensuring that equipment is properly set-up before polls open and minor issues are resolved throughout the day before they become major delays to voters. Focusing recruitment and training efforts into a small number of technical volunteers can reduce the number technical requests by resolving minor issues on-site and provide more time for mobile technical repair teams to address major issues. Consider the following distinctions between traditional and technical volunteer roles:
| Traditional volunteer | Technical volunteer |
|
|
Opportunities Beyond Election Day
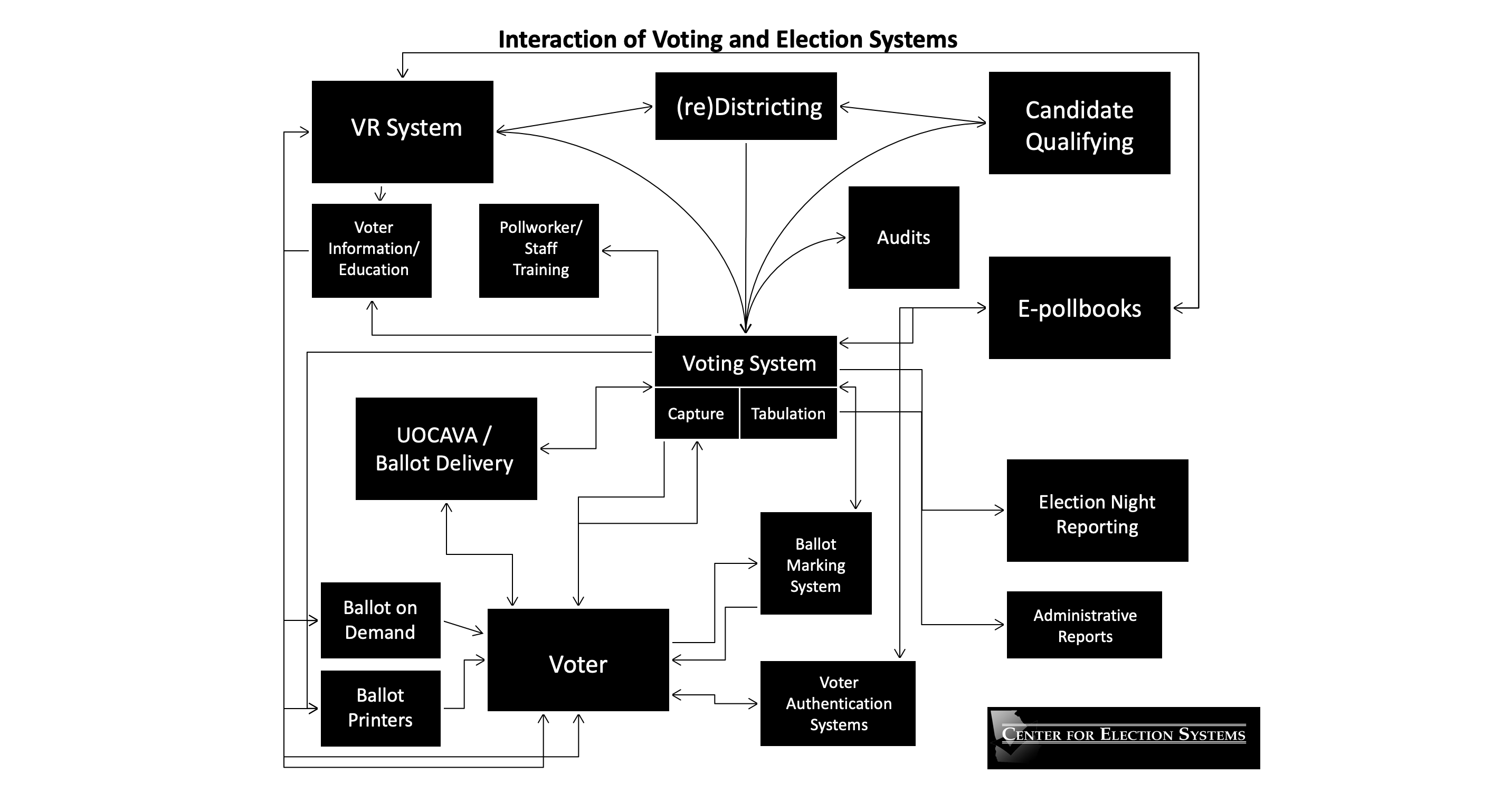
Election administration never stops. Election-related activities begin months before and continue months after Election Day. The focus on improving cybersecurity involves raising awareness about technical risks and driving change in the equipment, policies, and procedures of elections. Many jurisdictions, especially those without dedicated IT support, can benefit from integrating a small number of technical volunteers into those pre- and post-election activities. Supervised technical volunteers can be used to supplement internal staff or external contractors for basic to moderate tasks. There are numerous opportunities for technical volunteers to be useful supporting the complex interactions between voting and election systems.
Outreach in New Places
Every community has civic-minded infosec professionals that have the potential to make successful technical volunteers. The challenge is reaching these potential volunteers in non-traditional areas. Partnership with established organizations can help build institutional relationships based on trust and accountability, and provide a pipeline of technical expertise your volunteer pool.
- Schools (high schools, community colleges, technical schools, universities)
- Trade or professional associations
- Businesses
- Security conferences
- Targeted social media ads
Potential volunteers can refer to CDT’s Infosec Toolkit for Election Volunteering Toolkit to better understand the election process and volunteer roles.
Requirements for Vetting
Officials already have tried-and-true processes for vetting volunteers. Technical volunteers should go through those same vetting processes. In addition, consider how technical volunteers may be deployed and the additional assurances necessary to ensure the volunteer experience is specific and productive:
- Verify technical knowledge, skills, and abilities
- Identify specific tasks, projects, and outcomes
- Limit access to certain parts of the networks or databases
- Commit to clearly defined roles and responsibilities
- Seek legal guidance when in doubt about volunteer roles or backgrounds
Sample Statewide Models for Technical Support Deployment
For more information, please contact William T. Adler, CDT Senior Technologist, at [email protected], and Mallory Knodel, CDT Chief Technologist, at [email protected]. Additional election security resources: http://bit.ly/CDTelectsec.