Cybersecurity & Standards, Government Surveillance
Awaiting the Rushed Cyber Bill’s Final Language: What We Hope to See
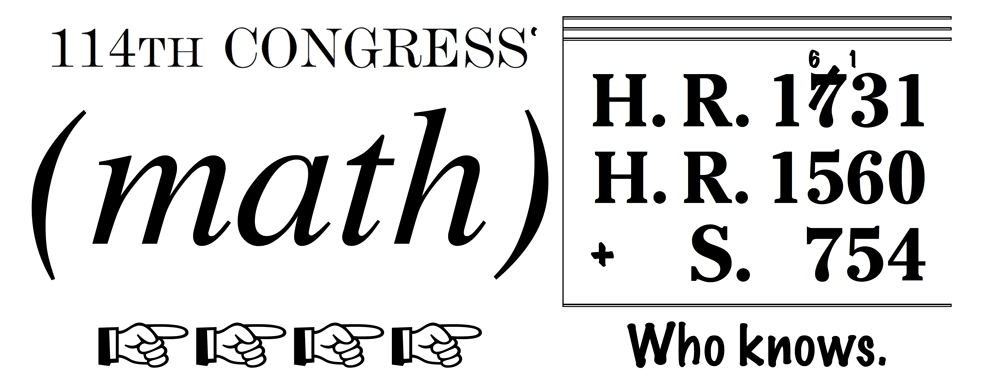
The final text of a cyber information sharing bill is expected to be released any minute now. The final bill will combine aspects of the Senate’s Cybersecurity Information Sharing Act (CISA-S.754), the House Intelligence Committee’s Protecting Cyber Networks Act (PCNA-H.R. 1560) and the House Homeland Security Committee’s National Cybersecurity Protection Advancement Act (NCPAA-H.R. 1731). According to recent reports, lawmakers hope to wrap up official conference negotiations (which have not yet begun) sometime this week, and expect to send the final bill to the President’s desk as part of an omnibus budget deal by the end of this year. The Center for Democracy & Technology is disappointed by the unnecessarily rushed, secretive process lawmakers turned to in order to reconcile the three bills. We hope that, in their haste, lawmakers managed to include crucial privacy protective measures in their final conference report.
According to publicly available information, instead of combining the three bills in an open, transparent manner, the Senate and House Intelligence Committees have been working together unofficially and created proposed final text as of last Friday, which they handed off to the House Homeland Security Committee for approval. Apparently Homeland Security staff pushed back because the bill lacked many of the NCPAA’s privacy protections, but Committee Chairman Michael McCaul (R-Texas) may be facing increasing pressure from House leadership to accept the deal and work to move a final version forward as quickly as possible.
Given the bill’s dubious cybersecurity value, we are confused by the sudden sense of urgency to pass the cyber information sharing bill, without carefully (and publicly) considering the various strengths and weaknesses of the three options. Regardless, when the final conference report is released, CDT hopes that it contains the following protective measures:
1. Establishing DHS as the Central Hub for Info Sharing: Unlike the Senate’s CISA and the House Intelligence Committee’s PCNA, the House Homeland Security’s NCPAA only permits companies to share information with the Department of Homeland Security. CDT supports this approach, because DHS is in the best position to scrub out sensitive personal information before that information is distributed to other federal agencies that are primarily focused on surveillance, not cybersecurity.
2. Limiting Dissemination, Retention, and Usage of Shared Info to Cyber Purposes Only: NCPAA is the only bill out of the three that limits the dissemination, retention, and usage of shared information to cybersecurity purposes. CDT hopes this commonsense restriction is in the final conference report, because it will ensure that the cyber information sharing program will be dedicated to its rightful purpose: cybersecurity, not backdoor surveillance.
3. Duty to Remove PII: The PCNA’s definition is the best out of the three: it requires entities to remove personally identifiable information (PII) before sharing cyber threat indicators (CTIs) upon “reasonable belief: that it is not “directly related” to a cybersecurity threat. Although an amendment from Senator Ron Wyden (D-Oregon) would have strengthened this privacy protection even further, this definition is currently the best option out there.
4. Strong Limitations on Countermeasures: CDT is concerned that each of the three bills fails to sufficiently prohibit countermeasures with negative external effects, which could potentially lead to a myriad of reckless activities detrimental to computer security. However, of the three bills, the Senate’s CISA contains the least destructive countermeasures language because it prohibits countermeasures that provide unauthorized access to data on another network.
CDT will provide its analysis of the final conference report once it is released. Stay tuned.


